Recently, I was working on a project that required Integration with Microsoft MFA using the Azure MFA NPS Plug-in.
Azure MFA worked fine and I followed this Citrix article to remove the secondary password field, but when users would logoff or go to a cached page, the second password field would be displayed. I found an article that discussed how to remove the second password field when integrating with DUO and I adapted it to work with Microsoft Azure MFA.
You will need to create rewrite polices using the following steps. (Thanks Duo for having a great step by step guide, which I used to Implement this for Azure MFA and to create this article).
Make sure that the rewrite policy is enabled on your Citrix Gateway, by going to System --> Settings --> Configure Basic Features and verify that the Rewrite Feature is checked.
- SSH into your Citrix Netscaler Gateway
- Enter the commands below to create a rewrite action that will hide the secondary password field.
- add rewrite action rw_act_insert_var_AZUREMFA_ENABLED insert_before_all "HTTP.RES.BODY(120000).SET_TEXT_MODE(IGNORECASE)" "\"var AZUREMFA_ENABLED = true;\"" -pattern "if (pwc ==2"
- add rewrite action rw_act_insert_AZUREMFA_ENABLED insert_after_all "HTTP.RES.BODY(120000).SET_TEXT_MODE(IGNORECASE)" "\" && !AZUREMFA_ENABLED\"" -pattern "if (pwc ==2
3. Then enter the following commands to create rewrite policies that apply the actions from the commands above to the gateway_login_form_view.js file.
- add rewrite policy rw_pol_insert_var_AZUREMFA_ENABLED "HTTP.REQ.URL.CONTAINS(\"gateway_login_form_view.js\")" rw_act_insert_var_AZUREMFA_ENABLED
- add rewrite policy rw_pol_insert_AZUREMFA_ENABLED "HTTP.REQ.URL.CONTAINS(\"gateway_login_form_view.js\")" rw_act_insert_AZUREMFA_ENABLED
4. In the Citrix Netscaler Gatway Admin Page go to Citrix Gateway --> Virtual Servers. Select the Virtual Server that has been enabled with Microsoft MFA Authentication.
5. Scroll down to Polices and click on the plus sign to add the MFA rewrite rules
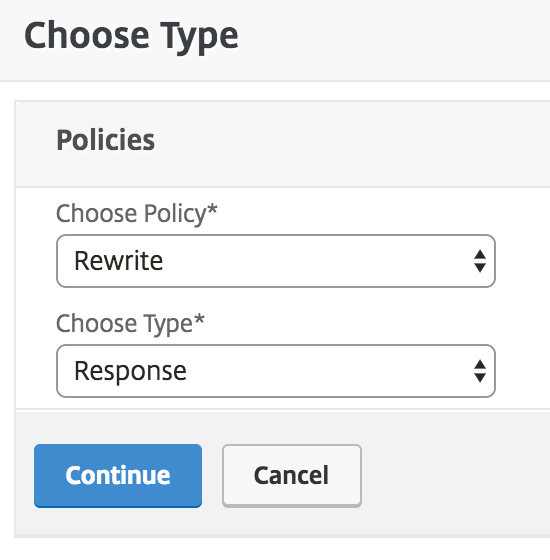
6. Select Rewrite from the choose type, select Response from the choose type dropdown. Click Continue.
7. On the next "Choose Type" page, click on the "Select Policy" Click to select field in the "Policy Binding" section of the page. This shows you the list of rewrite policies you created from the shell earlier.
Select the rw_pol_insert_var_AZUREMFA_ENABLED policy and click the Select button to return to the "Choose Type" page.
8. Back on the "Choose Type" page, change the "Goto Expression" to NEXT. You usually do not need to change the "Priority" from the default value assigned. Click the Bind button to bind the first rewrite policy to your virtual server.
9. Click on the Plus sign in Polices to bind the second MFA rewrite policy, choose policy Rewrite from the Choose Policy drop-down box and response from the choose type drop-down box and click continue
10. On the "Policy Binding page, click the Add Binding button. Click on the "Select Policy" Click to select field to bring up the list of policies. Select the rw_pol_insert_AZUREMFA_ENABLED policy and click the Select button to return to the "Policy Binding" page.
11. When back on the "Policy Binding" page, leave the "Goto Expression" set to END. You usually do not need to change the "Priority" from the default value assigned, just make sure that it has a greater number than the priority vaule assigned to the first bound policy (e.g. if the first one was priority 100 the second policy priority should be 110). Click the Bind button to bind the second rewrite policy to your virtual server.
12. Now you should see both "AZUREMFA_ENABLED" rewrite policies listed in the correct order (rw_pol_insert_var_AZUREMFA_ENABLED before rw_pol_insert_AZUREMFA_ENABLED). Click Close to finish.
13. Verify that you have two additional Rewrite policies listed under "Response Policies" and click Done.
14. Save all of the changes made to the running config.
Once this has been applied and users clear their browser cache, the secondary password filed should no longer display.
